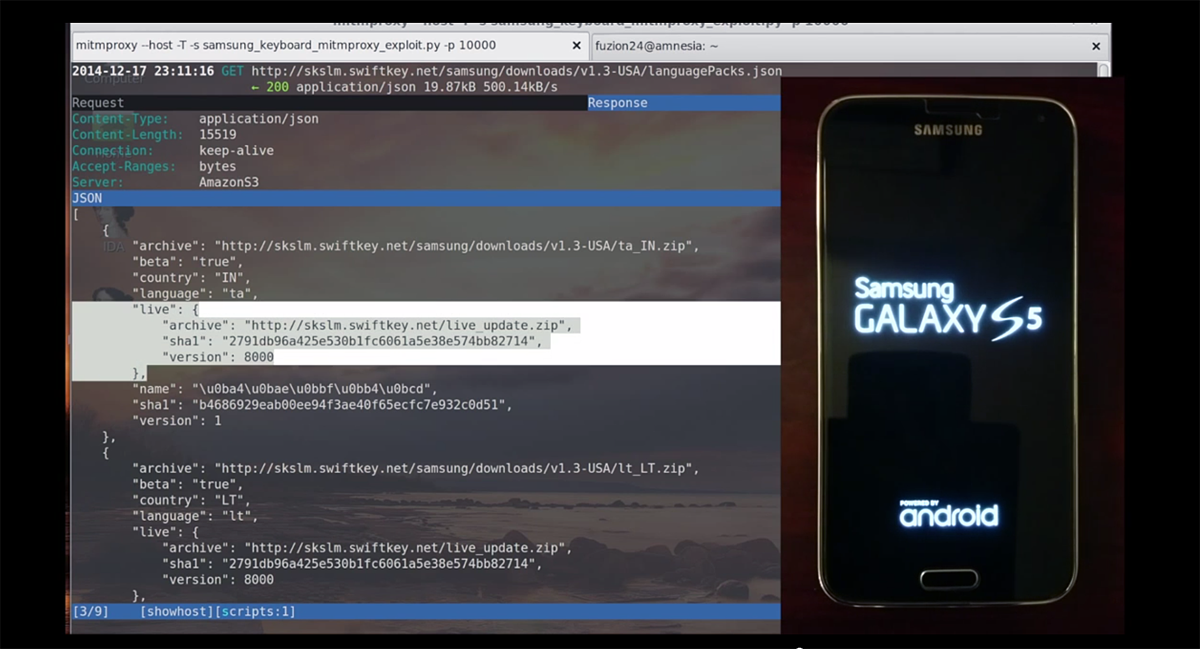
An example of a 'malicious archive file' aimed at vulnerability of long-established compression decompression software 'WinRAR' looks like this - GIGAZINE

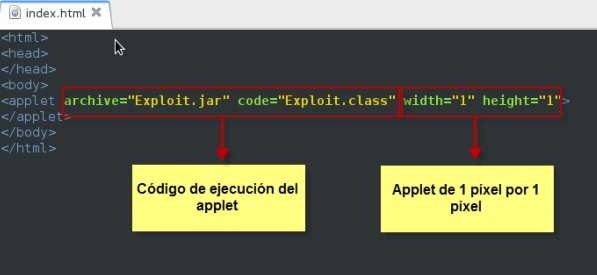
Structure et caractéristiques de l'archive exploitée. Structure and... | Download Scientific Diagram
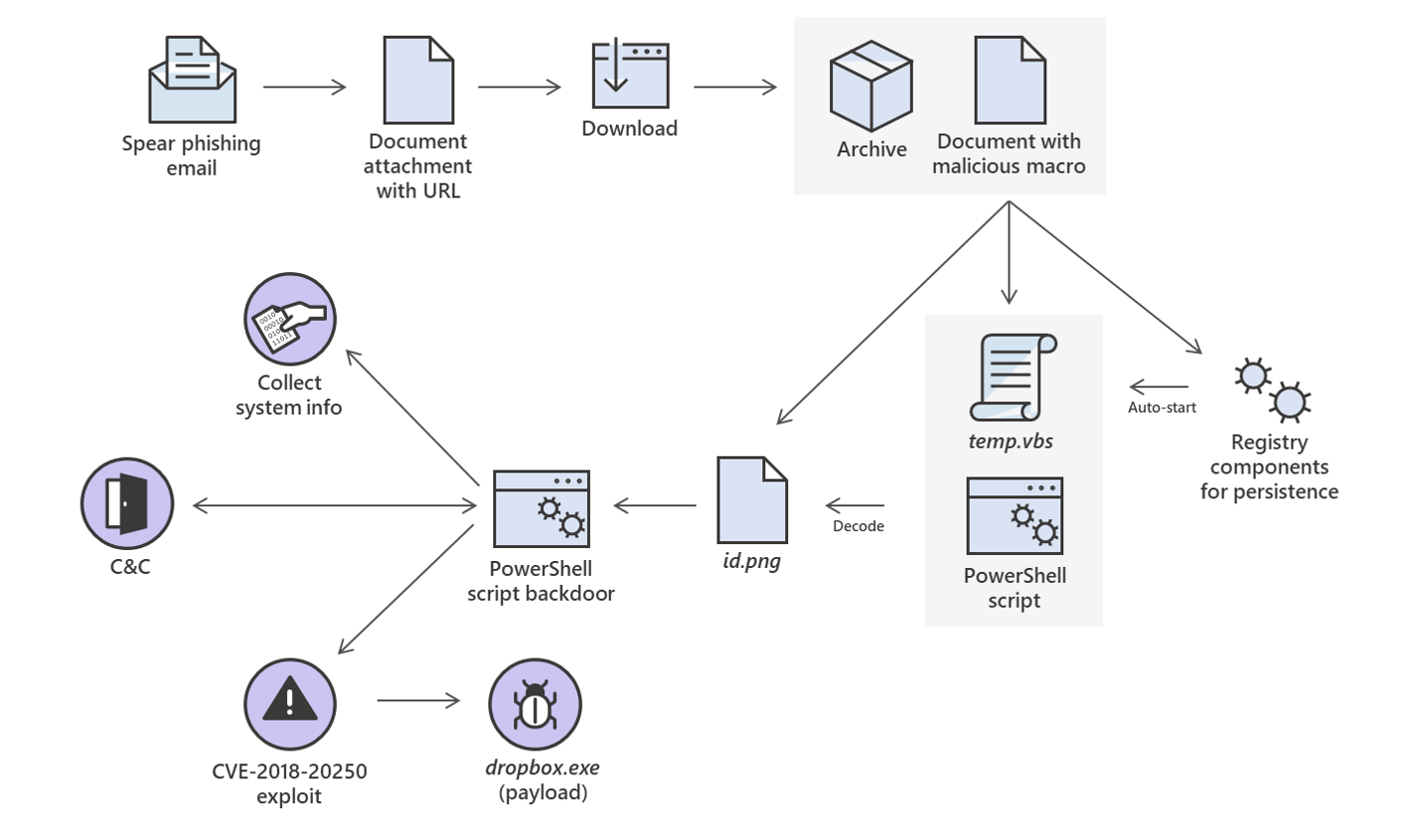
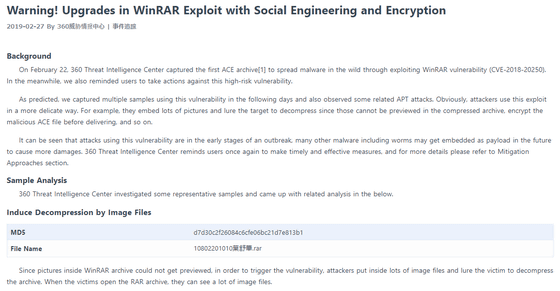
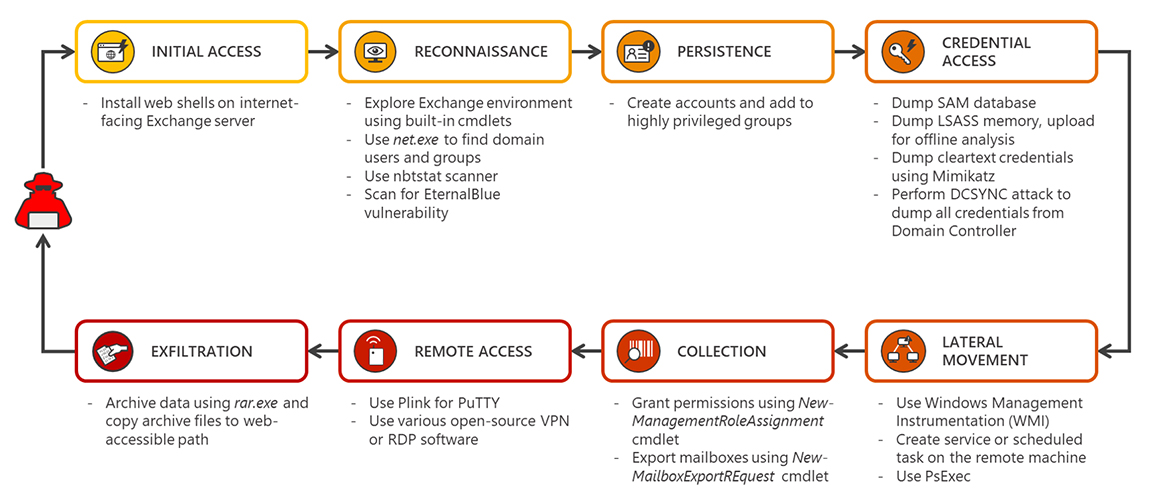
Analysis of a targeted attack exploiting the WinRAR CVE-2018-20250 vulnerability - Microsoft Security Blog

Edward's Exploit and Other Thomas the Tank Engine Stories (1993 Paperback Book) : Random House : Free Download, Borrow, and Streaming : Internet Archive







.png)